HIPAA Compliance for SaaS: Checklist and Requirements
Date
Apr 06, 26
Reading Time
11 Minutes
Category
SaaS Development
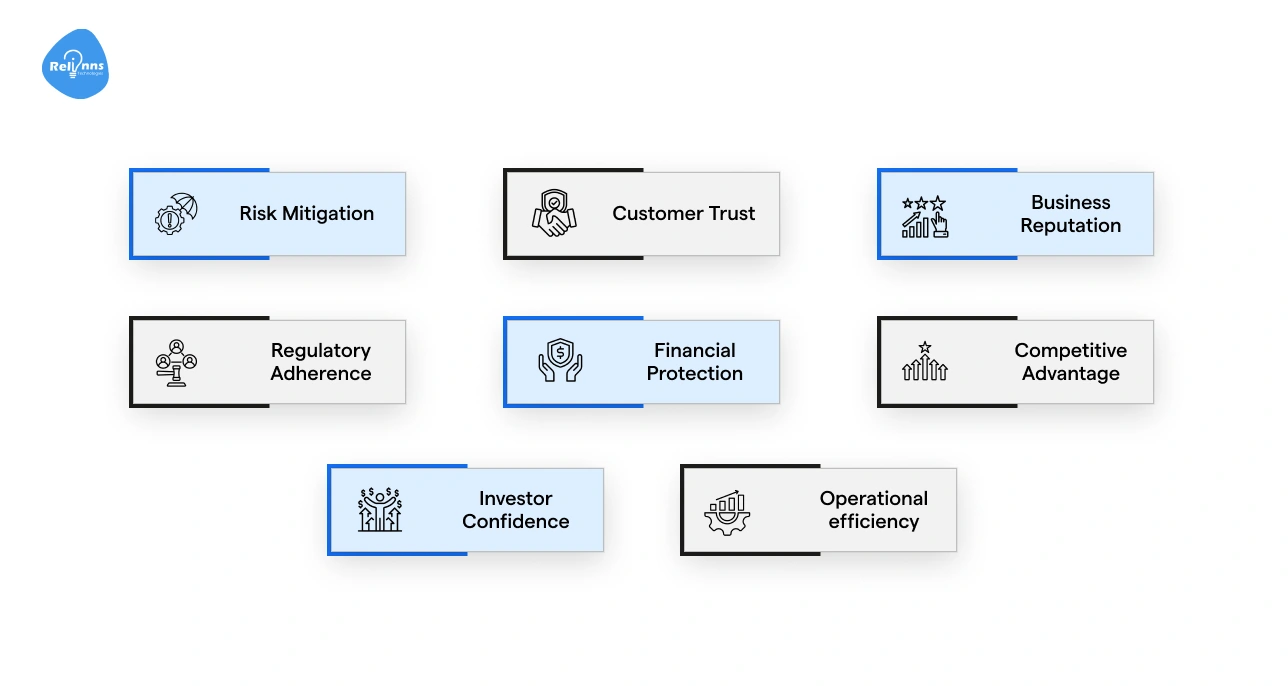
Most SaaS companies handling health data aren't fully HIPAA compliant. They just think they are.
That gap is dangerous. HIPAA doesn't grade on effort. It requires specific technical, administrative, and physical safeguards. Miss one, and you're exposed.
If you're building or scaling a healthcare SaaS product, compliance isn't optional. It's the foundation your entire product sits on.
In this guide, you’ll learn exactly what HIPAA compliance for SaaS means, who it applies to, and what you need to implement, with a clear checklist to get you there.
What HIPAA Compliance for SaaS Really Means
Health Insurance Portability and Accountability Act (HIPAA) compliance means your platform meets the legal requirements for handling protected health information (PHI). For SaaS companies, that means building security, privacy, and accountability directly into your product and operations.
It's not a certification you earn once. It's an ongoing responsibility.
The need for HIPAA is well felt in the sheer scale of healthcare data exposure across the U.S. In fact, American healthcare organizations recorded 710 large-scale data breaches in a single year, each resulting in the loss of over 500 records. (Source: Statista)
Simply put, if your platform touches patient data, HIPAA applies to you. No exceptions.
Do You Need HIPAA Compliance for Your SaaS? What You Should Know
HIPAA doesn't just apply to hospitals. If your SaaS platform interacts with PHI in any way, you likely have compliance obligations too.
Here are some main entities (except primary healthcare providers like hospitals & clinics) that need to be careful about HIPAA:
Healthcare SaaS Providers Handling ePHI
EHR systems, patient portals, telehealth tools, and billing platforms all handle electronic protected health information (ePHI) directly. These platforms typically operate as business associates under HIPAA.
Example: A telehealth startup that stores video consultation records or a billing tool that processes insurance claims
Business Associates and Subprocessors
If you provide services to a covered entity (like a hospital or clinic) and access their patient data, you're a business associate.
That includes cloud storage providers, analytics tools, and AI platforms. Subcontractors supporting these systems may also fall under HIPAA requirements.
As healthcare platforms grow more data-driven, many providers rely on experienced healthcare technology teams like Relinns Technologies to build AI-powered systems that handle patient data securely while aligning with HIPAA safeguards and compliance requirements.
HIPAA for IT Service Providers and Technology Vendors
Managed service providers, DevOps vendors, and AI solution providers handling health data fall under HIPAA, too (even if healthcare isn't your primary market).
Think of it as indirect exposure; you're not the one treating patients, but you're holding the keys to their data.
When SaaS Companies May Not Fall Under HIPAA
Having discussed who falls under HIPAA, we must also recognize the platforms that shouldn't worry about these obligations. If your platform never stores, processes, or transmits PHI, and you do not have contracts with HIPAA-covered entities, the regulation may not apply.
However, companies should verify this carefully before assuming they are exempt, especially when expanding into healthcare markets.
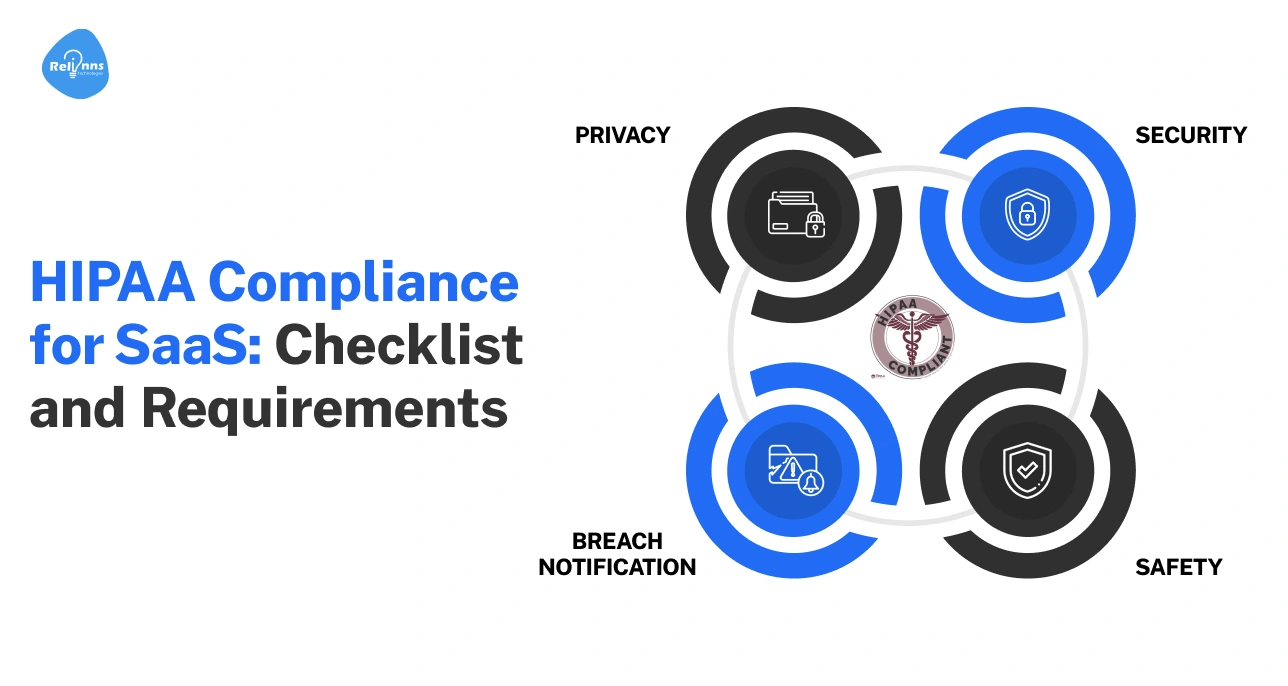
HIPAA Rules for SaaS: Privacy, Security, and Breach Rules
HIPAA compliance for SaaS is built around three core rules. Essentially, if a SaaS platform stores or processes ePHI, its systems and policies must align with these requirements.
Here’s a breakdown of the HIPAA rules that define how healthcare data should be used, protected, and reported if compromised.
Next, we’ll break down each rule so it’s easy to understand.
HIPAA Privacy Rule
The Privacy Rule is a baseline standard that controls how patient data can be accessed and disclosed. It involves patient rights, permitted data use, and disclosure limitations.
Key points for SaaS platforms:
- Follow the minimum necessary rule when accessing PHI, which states that only the data needed for a specific task should be used.
- Allow patients to access their data or request corrections, ensuring transparency and control.
- Define clear data handling and disclosure policies. If a business associate has access to PHI, then it must follow these policies and agreements strictly.
HIPAA Security Rule
This rule protects ePHI through required safeguards. The main goal of this rule is to ensure the confidentiality, integrity, and availability of patient data.
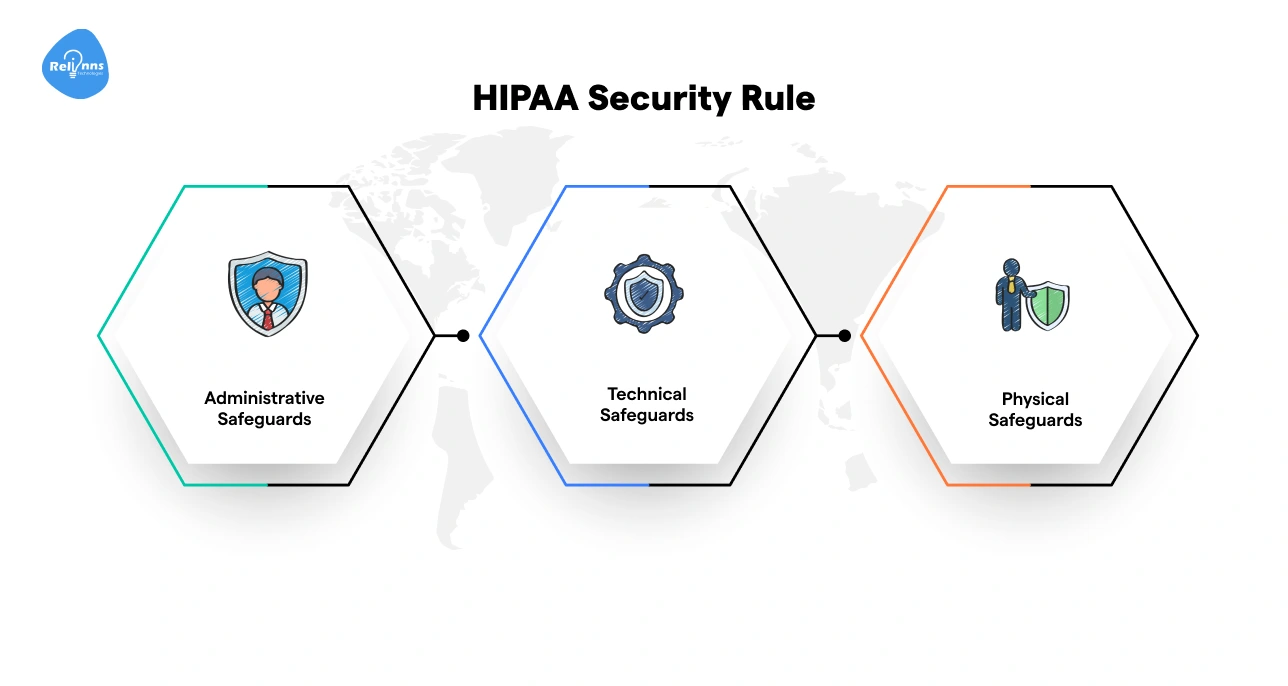
The HIPAA Security Rule includes three safeguard categories:
- Administrative Safeguards: Risk assessments, policies, workforce training
- Technical Safeguards: Access control, encryption, audit logs
- Physical Safeguards: Facility security and device protection
HIPAA Breach Notification Rule
This rule defines how organizations must respond when PHI is compromised.
For example, if patient records are accessed by an unauthorized person or a system containing PHI is hacked, the organization must report the incident within the stipulated period.
Key requirements include:
- Investigating suspected security incidents, like data breaches and unauthorized access
- Notifying affected individuals and regulators
- Reporting breaches within 60 days of discovery
These rules constitute the compliance requirements for healthcare SaaS companies handling healthcare data.
HIPAA Compliance Checklist for Healthcare SaaS Platforms
If you're building a cloud-native healthcare SaaS product, HIPAA compliance isn't a one-time audit. It's a set of ongoing operational practices.
Use this HIPAA software compliance checklist as your baseline.
Key Takeaways:
- Electronic PHI can live in more places than you think - databases, logs, backups, and third-party tools all count. Map where it lives and how it moves before doing anything else.
- Encryption and access controls are your first line of defense: AES-256 at rest, TLS 1.2+ in transit, and least-privilege access across every role.
- Audit logs are your compliance proof; log every access, edit, and deletion with timestamps and user IDs. If it's not logged, it didn't happen.
- Have a breach response plan ready before you need it, and keep your team trained, reviewed, and documented on a regular cadence.
HIPAA Software Requirements: What You Need to Build In
The software itself must include security features that protect patient information at every stage, from login to storage and system monitoring.
The HIPAA software requirements given below help you stay compliant, avoid costly violations, and maintain patient trust.
Access Controls and User Authentication
Every user should have clearly defined permissions. Not everyone in an organization needs the same level of access to patient data.
For example, a doctor may view medical records, while a billing team member only sees payment information.
Strong login protections, such as multi-factor authentication, also help prevent unauthorized access.
Encryption for Data at Rest and in Transit
Patient data must be protected whether it is stored or moving between systems. Encryption ensures that even if someone intercepts the data, it cannot be read.
For instance, medical files stored in a database should be encrypted, and data sent between a mobile health app and a cloud server should travel through secure protocols.
Audit Logs and Activity Tracking
If something goes wrong, audit logs are your first line of defense. Your platform must record every ePHI interaction (user ID, timestamp, action taken, and access point).
No logs means no evidence. And in a HIPAA audit, no evidence means non-compliance.
Data Backup, Recovery, and Availability
Systems should regularly back up patient information and provide reliable recovery options. If a server fails or a cyberattack occurs, healthcare providers must still be able to access critical records.
Workforce Policies and Security Training
Technology alone is not enough. Employees must understand how to handle sensitive data, recognize phishing attempts, and follow security procedures.
Consider this: One of the most common HIPAA violations isn't a cyberattack; it's an employee emailing an unencrypted patient file to the wrong recipient.
Infrastructure and Physical Security
Cloud servers, data centers, and hardware must be protected with strict security controls. This includes controlled facility access, monitoring systems, and secure hosting environments.
Keeping your platform compliant is like running a hospital itself. Every department, every process, and every person plays a role. One weak link puts the whole system at risk.
Required vs Addressable HIPAA Safeguards: What's the Difference?
Under the HIPAA Security Rule, safeguards fall into two categories: required and addressable.
The difference is simple. Required safeguards must always be implemented. Addressable safeguards allow flexibility depending on risk and system design.
The table below breaks down both categories with real-world examples, so you know exactly where you have flexibility and where you don't.
Thus, being addressable doesn't mean being optional; it means being deliberate and documented.
How SaaS Companies Implement Addressable Controls
In practice, SaaS companies perform risk assessments before deciding how to apply addressable safeguards.
Practical Example: HIPAA lists encryption of data at rest as an addressable safeguard. Most healthcare SaaS platforms implement strong encryption, such as AES-256, across databases and storage systems to protect ePHI.
However, HIPAA allows flexibility in how safeguards are implemented. A company might use cloud provider encryption, application-level encryption, or key management systems, depending on its architecture and risk profile.
The key requirement is documentation. If a company chooses not to implement a safeguard in a specific way, it must document the reasoning and ensure alternative controls provide comparable protection.
Business Associate Agreements: The HIPAA Contract Every SaaS Company Needs
A Business Associate Agreement (BAA) defines how data must be protected.
Healthcare SaaS companies often work with hospitals, clinics, and other vendors that handle patient data. When ePHI is shared, a Business Associate Agreement is required.
When SaaS Companies Must Sign a BAA
A SaaS company must sign a BAA when it stores, processes, or transmits ePHI on behalf of a healthcare provider.
For example, a telehealth platform hosting patient records for a hospital must have a BAA in place before handling that data.
Vendors and Partners That Require BAAs
BAAs are also required with vendors that support your platform and may access ePHI, directly or indirectly. Common examples include:
- Cloud hosting providers
- Analytics and monitoring platforms
- Customer support and ticketing tools
- Email and communication services
- Backup and disaster recovery providers
What a HIPAA-Compliant BAA Should Include
A BAA isn't just a formality; it's a binding document that defines exactly how patient data will be handled.
At a minimum, it should cover permitted uses of ePHI, each party's security responsibilities, breach notification timelines, and what happens to data when the agreement ends.
Responsibilities After Signing a BAA
Signing a BAA doesn't close the loop - it opens one. Both parties are now legally bound to uphold every security practice defined in the agreement.
That means protecting patient data at all times, reporting incidents promptly, and keeping compliance controls current as your platform evolves.
In HIPAA compliance, a BAA isn't just a contract; it's your last line of legal defense.
HIPAA Violations Waiting to Happen: Common SaaS Compliance Mistakes
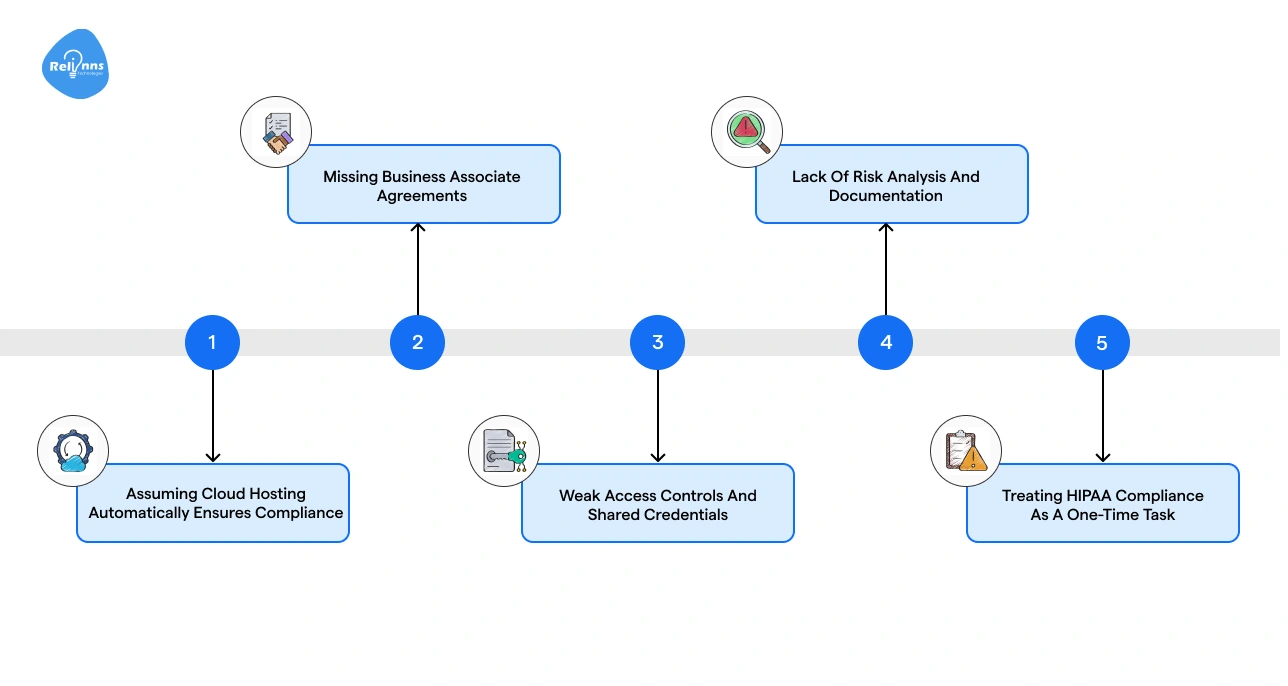
HIPAA compliance can be challenging for SaaS companies, especially when systems grow quickly and multiple vendors are involved. Many compliance issues arise not from complex technology but from simple oversights.
Understanding these common mistakes can help teams prevent costly violations and protect patient data.
Assuming Cloud Hosting Automatically Ensures Compliance
Mistake: Some SaaS companies assume that hosting their platform on a major cloud provider automatically makes their system HIPAA compliant. This is one of the most dangerous misconceptions in healthcare SaaS, and one of the most common.
How to avoid it: Cloud providers only secure the infrastructure. Your team must still configure access controls, encryption, logging, and policies to protect patient data properly.
Missing Business Associate Agreements
Mistake: Handling ePHI without signing BAAs with healthcare clients or third-party vendors invites direct regulatory liability and leaves both parties legally exposed in the event of a breach.
How to avoid it: Ensure BAAs are signed with all partners who may store, process, or access patient data, including hosting providers and service vendors.
Weak Access Controls and Shared Credentials
Mistake: Teams sometimes share accounts or grant broad system access to multiple employees. This creates an unauditable trail, making it nearly impossible to detect unauthorized access or investigate a breach.
How to avoid it: Use unique user credentials, role-based permissions, and multi-factor authentication so only authorized users can access sensitive data.
Lack of Risk Analysis and Documentation
Mistake: Skipping formal risk assessments or failing to document security practices doesn't just leave gaps in your compliance posture but also eliminates your ability to defend yourself during an audit.
How to avoid it: Conduct regular risk analyses and maintain clear documentation of policies, security controls, and compliance measures.
Treating HIPAA Compliance as a One-Time Task
Mistake: Some organizations treat compliance as a one-time setup instead of an ongoing responsibility.
How to avoid it: Continuously review systems, update policies, train staff, and monitor security controls to maintain long-term compliance.
Most HIPAA violations don't start with a cyberattack. They start with an assumption, a skipped step, or a contract that was never signed.
How to Vet a HIPAA-Compliant SaaS Vendor Before You Sign Anything
Choosing the right SaaS vendor is critical for protecting patient data. Not every vendor that claims HIPAA support actually meets compliance requirements.
A quick evaluation of security practices, documentation, and responsibilities can help healthcare teams make safer decisions.
Security and Compliance Questions to Ask
Before selecting a vendor, ask clear questions about how they protect patient data. These may look like:
- Do you sign a Business Associate Agreement (BAA)?
- How is ePHI encrypted in storage and during transmission?
- What access controls and authentication methods are used?
- Are audit logs and monitoring tools in place?
- How are security incidents detected and reported?
Documents and Evidence Vendors Should Provide
A trustworthy vendor should be able to share proof of their security practices:
- Signed Business Associate Agreement
- Security policies and compliance documentation
- Risk assessment reports
- Audit logs or monitoring capabilities
- Relevant security certifications or compliance reports
HIPAA Compliant vs HIPAA Eligible Software
Not all software used in healthcare is automatically HIPAA compliant. Some platforms simply provide the tools needed to build compliant systems.
In short: Compliant software actively supports HIPAA requirements, while eligible software only provides the infrastructure to build compliant systems.
Many healthcare organizations choose to trust specialized healthcare technology partners, such as Relinns Technologies, to build AI-powered healthcare platforms designed with HIPAA safeguards, secure data handling, and BAA-ready infrastructure from the start.
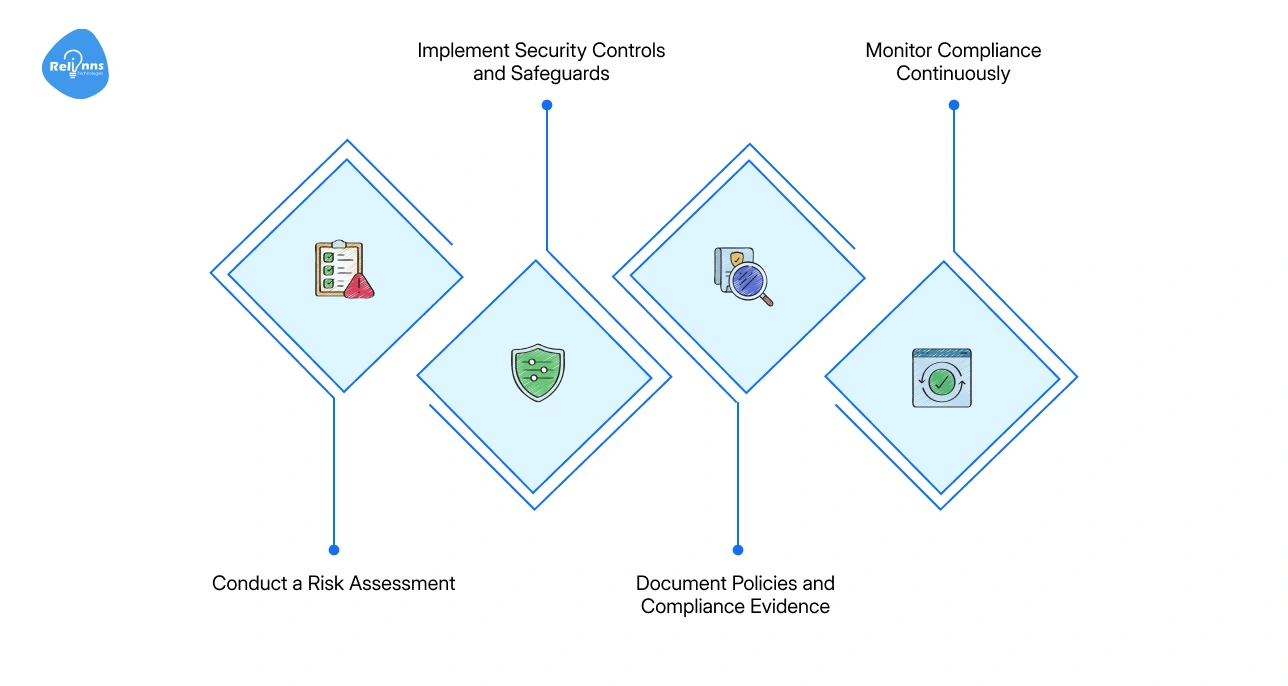
How SaaS Companies Can Start Building a HIPAA Compliance Program
Starting HIPAA compliance doesn't have to be overwhelming. Focus on these core steps to protect patient data and build a strong foundation from day one.
Conduct a Risk Assessment
Start by mapping where ePHI lives; how it's stored, where it moves, and who can access it. Review your systems, data flows, and third-party vendors to surface potential vulnerabilities before they become violations.
Implement Security Controls and Safeguards
Once risks are identified, close the gaps. Enforce role-based access, encrypt data at rest and in transit, enable audit logging, and require multi-factor authentication across all systems that touch patient data.
Document Policies and Compliance Evidence
Good security without documentation is invisible to an auditor. Define clear policies for handling ePHI, record every control you've implemented, and maintain a paper trail of risk assessments and compliance decisions.
Monitor Compliance Continuously
Threats evolve, systems change, and teams grow. Schedule regular reviews, update policies as your platform scales, and keep employee training current. Compliance isn't a destination; it's an operating standard.
Final Thoughts
HIPAA compliance for SaaS is not just a legal requirement. It is a core part of building trustworthy healthcare software. If your platform handles patient data, you must protect it through strong safeguards, clear policies, and continuous monitoring.
Start by understanding where ePHI lives and how it moves through your systems. Put the right controls in place. Document every decision and security practice.
Strong compliance builds trust with healthcare providers and patients. When security and privacy are built into your product from the start, your platform is better prepared to operate, grow, and handle sensitive healthcare data responsibly.
Frequently Asked Questions (FAQs)
What is HIPAA compliance for SaaS?
HIPAA compliance for SaaS means building systems, policies, and safeguards that protect electronic protected health information (ePHI) when storing, processing, or transmitting patient data.
Do SaaS companies need to be HIPAA compliant?
Yes. SaaS companies must follow HIPAA if their platform stores, processes, or transmits protected health information on behalf of healthcare providers or other covered entities.
What are the key HIPAA requirements for SaaS platforms?
Key requirements include access controls, encryption for data at rest and in transit, audit logging, risk assessments, employee training, breach response procedures, and signed Business Associate Agreements.
What is a Business Associate Agreement (BAA)?
A Business Associate Agreement is a legal contract that defines how a SaaS provider and healthcare organization will protect, use, and report incidents involving patient data.
What happens if a SaaS company violates HIPAA?
HIPAA violations can lead to heavy fines, legal action, mandatory corrective measures, and reputational damage if patient data is exposed or security safeguards are not properly implemented.
Is using a cloud provider enough to make SaaS HIPAA compliant?
No. Cloud providers only secure infrastructure. SaaS companies must still configure encryption, access controls, logging, policies, and compliance processes to meet HIPAA requirements.
How can a SaaS startup start HIPAA compliance?
Start by identifying where ePHI is stored, conducting risk assessments, implementing encryption and access controls, signing BAAs with vendors, documenting policies, and monitoring security continuously.